General Purpose HSM
■ Product Introduction and Features
General Purpose HSM is a type of fundamental cryptographic device independently developed by Sansec. It adapts to vairous kinds of cryptographic security systems. It can ensure the confidentiality, integrity, and effectiveness of the transmitted information through its digital signature and encryption function. These functions are achieved by its high-speed and multi-task parallel processing cryptographic operation.
It has been applied to e-government, e-commerce and enterprise information systems such as online approval, office, banking, securities and online payment. This provides a security guarantee for the development of social informatization.

■ Application Scenario
Cryptographic Algorithm Support
Chinese cryptographic algorithm: SM1, SM2, SM3 and SM4
International cryptographic algorithm: RSA, 3DES, AES, SHA1 and SHA2
Key Management
Key generation (Level 2 and 3 commercial cryptographic modules certified by State Cryptography Administration), storage, backup, and restoration.
Random Number Generation
Adopt the dual physical random number generation chip approved by the OCSSA to generate random numbers
User Access Control
Hierarchical management of access users to improve the security of HSM
Support Standard Interface
The API interface supports the GM/T0018-2012 Specifications of Cryptography Device Application Interface standard, and supports international interface standards such as PKCS#11, MS-CSP, JCE, etc.
Multi-parallel
Improve the performance of cryptographic operations
Fault tolerance, which does not affect business when a HSM fails.
■ Product Functions

System security
HSM realizes the authorization and authentication to the application server through the support of crypto connection and whitelist, which further improve the security of the system.

Key Security
Adopt the three-layer key structure: "System Protection Key-User Key-Session Key" to thoroughly guarantee the security of keys and application systems.

Compliance
Adopt hardware cryptographic modules (meet the requirements of security level 2 and level 3 approved by OCSSA).
标准化
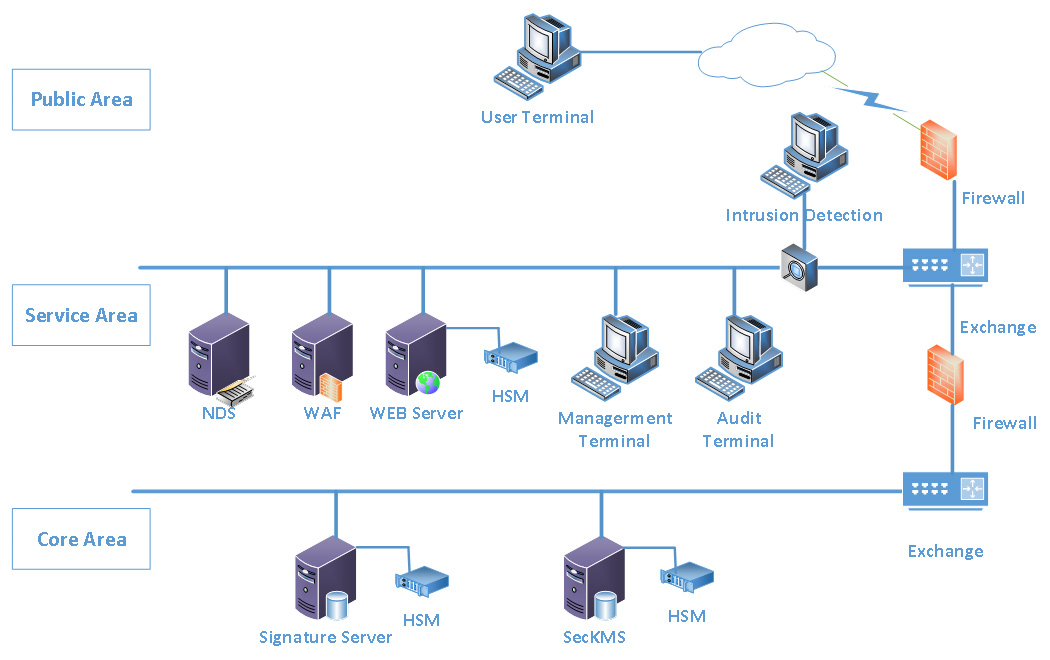
■ Application Diagram
■ 产品规格
|
产品型号 |
SecHSM-Net 310 |
SecHSM-Net 510 |
SecHSM-Net 710 |
|
外观规格 |
2U |
2U |
2U |
|
电源 |
冗余电源(可选) |
冗余电源(可选) |
冗余电源 |
|
网络接口 |
RJ-45 10/100/1000Mb x2 |
RJ-45 10/100/1000Mb x2 |
RJ-45 10/100/1000Mb x2 |
|
MTBF |
50000小时 |
50000小时 |
50000小时 |
|
工作协议 |
TCP/IP |
TCP/IP |
TCP/IP |
注:仅供参考,实际交付以合同为准